PDF] Malware Detection and Removal: An examination of personal anti-virus software
Por um escritor misterioso
Last updated 07 junho 2024
![PDF] Malware Detection and Removal: An examination of personal anti-virus software](https://d3i71xaburhd42.cloudfront.net/3854f4d4217f9340348342f5764e3d6c84779101/4-Table2-1.png)
Examination of the quality of malware removal programs currently available on the market suggests that current anti-virus products, whilst able to detect most recently released malware, still fall short of eliminating the malware and returning the system to its original state. SoHo users are increasingly faced with the dilemma of applying appropriate security mechanisms to their computer with little or no knowledge of which countermeasure will deal with which potential threat. As problematic as it may seem for individuals to apply appropriate safeguards, individuals with malicious intent are advancing methods by which malicious software may operate undetected on a target host. Previous research has identified that there are numerous ways in which malware may go undetected on a target workstation. This paper examines the quality of malware removal programs currently available on the market, which consumers may use whilst utilising the Internet. The research suggests that current anti-virus products, whilst able to detect most recently released malware, still fall short of eliminating the malware and returning the system to its original state. The paper does not compare or disclose potential flaws within each product; rather it depicts the current state of anti-virus products.
![PDF] Malware Detection and Removal: An examination of personal anti-virus software](https://pub.mdpi-res.com/sustainability/sustainability-14-00008/article_deploy/html/images/sustainability-14-00008-g001.png?1640074725)
Sustainability, Free Full-Text
![PDF] Malware Detection and Removal: An examination of personal anti-virus software](https://pub.mdpi-res.com/symmetry/symmetry-14-02304/article_deploy/html/images/symmetry-14-02304-g001.png?1667645062)
Symmetry, Free Full-Text
![PDF] Malware Detection and Removal: An examination of personal anti-virus software](https://i1.rgstatic.net/publication/269399065_A_LITERATURE_REVIEW_ON_MALWARE_AND_ITS_ANALYSIS/links/562081f208ae93a5c9243f4b/largepreview.png)
PDF) A LITERATURE REVIEW ON MALWARE AND ITS ANALYSIS
![PDF] Malware Detection and Removal: An examination of personal anti-virus software](https://cdn.ttgtmedia.com/rms/onlineimages/whatis-malware_types_mobile.png)
What is Antivirus Software?
![PDF] Malware Detection and Removal: An examination of personal anti-virus software](https://www.mdpi.com/symmetry/symmetry-14-02308/article_deploy/html/images/symmetry-14-02308-g001.png)
Symmetry, Free Full-Text
![PDF] Malware Detection and Removal: An examination of personal anti-virus software](https://i.pcmag.com/imagery/articles/06EQOxrgTO3mqPNBMZdjHQ8-11.fit_lim.size_1050x.png)
How to Remove Malware From Your PC
![PDF] Malware Detection and Removal: An examination of personal anti-virus software](https://www.mdpi.com/electronics/electronics-12-04299/article_deploy/html/images/electronics-12-04299-g001-550.jpg)
Electronics, Free Full-Text
![PDF] Malware Detection and Removal: An examination of personal anti-virus software](https://media.springernature.com/m685/springer-static/image/art%3A10.1038%2Fs41598-022-05921-5/MediaObjects/41598_2022_5921_Fig1_HTML.png)
Antivirus applied to JAR malware detection based on runtime behaviors
![PDF] Malware Detection and Removal: An examination of personal anti-virus software](https://www.security.org/app/uploads/2020/12/ESET-Dashboard-Main.png)
How Does Antivirus Software Work?
![PDF] Malware Detection and Removal: An examination of personal anti-virus software](https://socradar.io/wp-content/uploads/2023/07/virustotal-1024x498.png)
Top 10 Malware Analysis Platforms & Tools
![PDF] Malware Detection and Removal: An examination of personal anti-virus software](https://academy.avast.com/hubfs/academy%20security/Image%20object%20-%20Media%20section%20(17).png)
Free Anti-Spyware Software, Scan & Remove Spyware
![PDF] Malware Detection and Removal: An examination of personal anti-virus software](https://i.pcmag.com/imagery/reviews/02uzazyH3C1xNU8CEqB10Ue-27..v1597339266.png)
Kaspersky Anti-Virus Review
![PDF] Malware Detection and Removal: An examination of personal anti-virus software](https://i1.rgstatic.net/publication/282247734_Malware_Detection_Supportive_Software_Agents_and_Its_Classification_Schemes/links/56099edf08ae1396914a256d/largepreview.png)
PDF) Malware Detection, Supportive Software Agents and Its Classification Schemes
![PDF] Malware Detection and Removal: An examination of personal anti-virus software](https://i.pcmag.com/imagery/articles/06EQOxrgTO3mqPNBMZdjHQ8-12..v1603305119.jpg)
How to Remove Malware From Your PC
![PDF] Malware Detection and Removal: An examination of personal anti-virus software](https://www.pcrisk.com/images/stories/screenshots202301/pdf-ransomware-encrypted-files.jpg)
Pdf Ransomware - Decryption, removal, and lost files recovery (updated)
Recomendado para você
-
 IKARUS anti.virus Manual - Ikarus Software GembH07 junho 2024
IKARUS anti.virus Manual - Ikarus Software GembH07 junho 2024 -
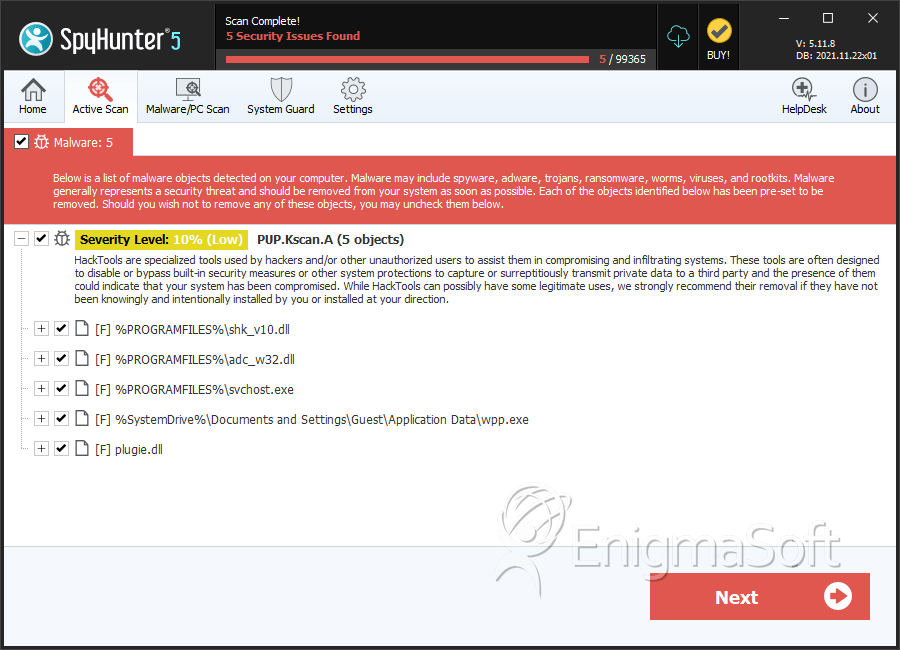 Trojan:Win32/FakeScanti Removal Report07 junho 2024
Trojan:Win32/FakeScanti Removal Report07 junho 2024 -
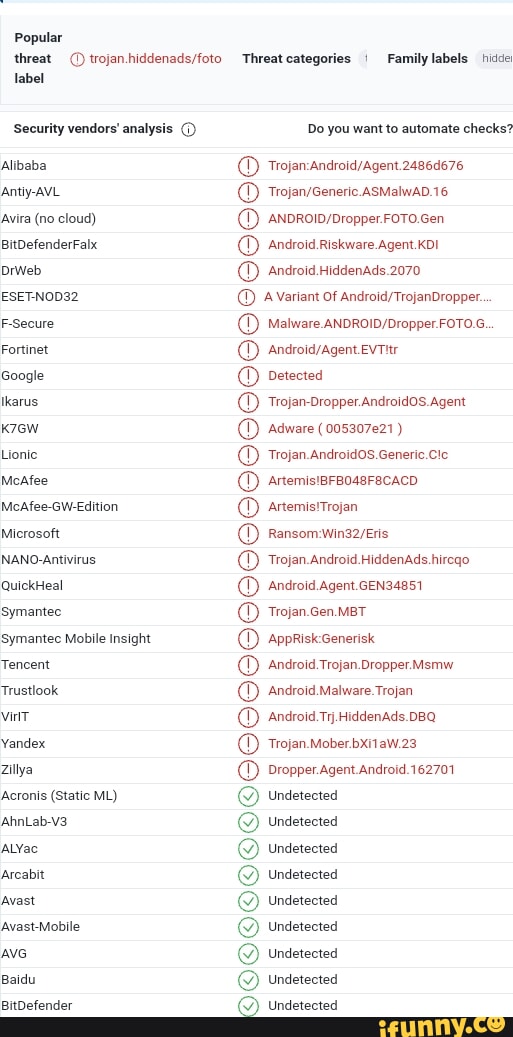 Ikarus memes. Best Collection of funny Ikarus pictures on iFunny Brazil07 junho 2024
Ikarus memes. Best Collection of funny Ikarus pictures on iFunny Brazil07 junho 2024 -
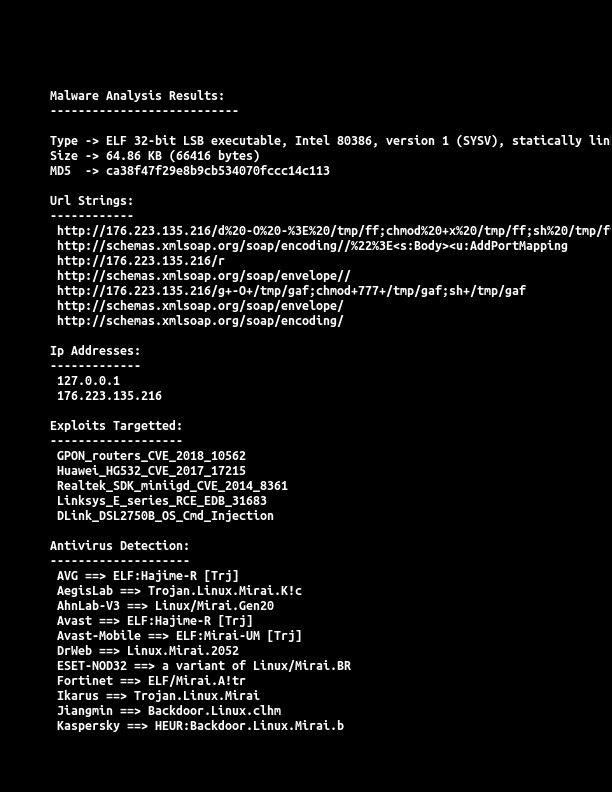 R. on X: Again #RIFT #IoT #Botnet #Mirai #ELF #malware #Trojan.Linux #Backdoor Exploit Target : #GPON #HUAWEI #REALTEK #Linksys #DLINK 𝗜𝗣: 176.223.135(.)216 Payload 𝗟𝗜𝗡𝗞: 176.223.135.216/bins/rift.* Country: Poland Currently 𝗔𝗰𝘁𝗶𝘃𝗲 CC: @_07 junho 2024
R. on X: Again #RIFT #IoT #Botnet #Mirai #ELF #malware #Trojan.Linux #Backdoor Exploit Target : #GPON #HUAWEI #REALTEK #Linksys #DLINK 𝗜𝗣: 176.223.135(.)216 Payload 𝗟𝗜𝗡𝗞: 176.223.135.216/bins/rift.* Country: Poland Currently 𝗔𝗰𝘁𝗶𝘃𝗲 CC: @_07 junho 2024 -
 Trojan Minibus. Commercial vehicle, Bus coach, Trojan07 junho 2024
Trojan Minibus. Commercial vehicle, Bus coach, Trojan07 junho 2024 -
 City of Troy Greek Mythology Travel Print Trojan Horse - Norway07 junho 2024
City of Troy Greek Mythology Travel Print Trojan Horse - Norway07 junho 2024 -
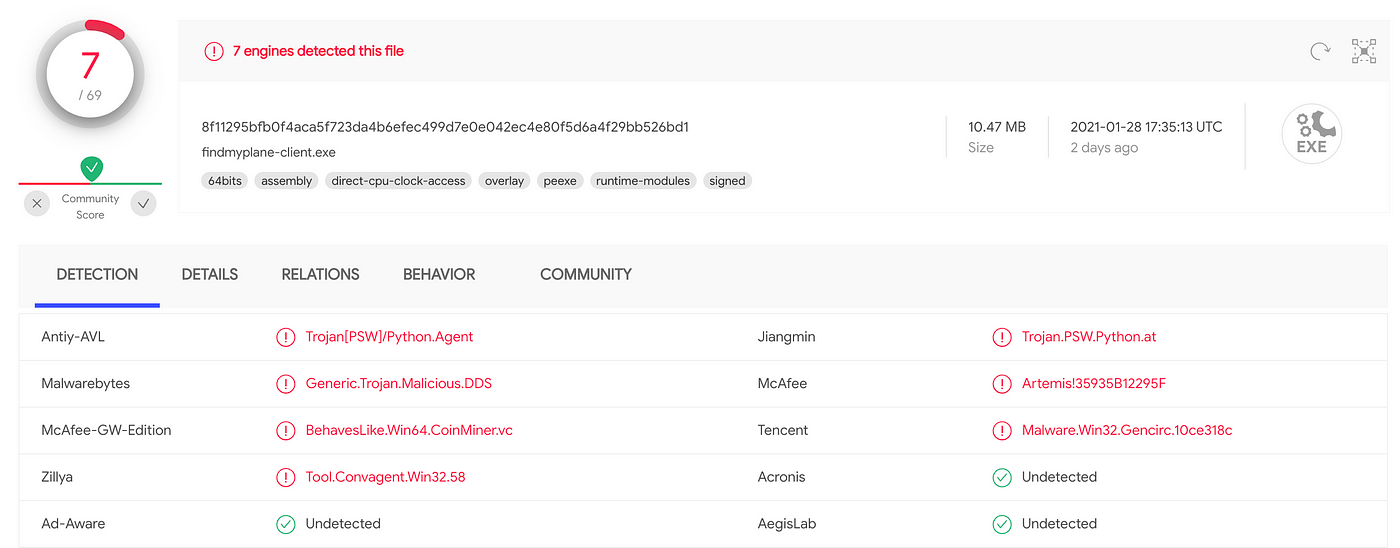 How to stop your Python programs being seen as malware, by Mark Hank07 junho 2024
How to stop your Python programs being seen as malware, by Mark Hank07 junho 2024 -
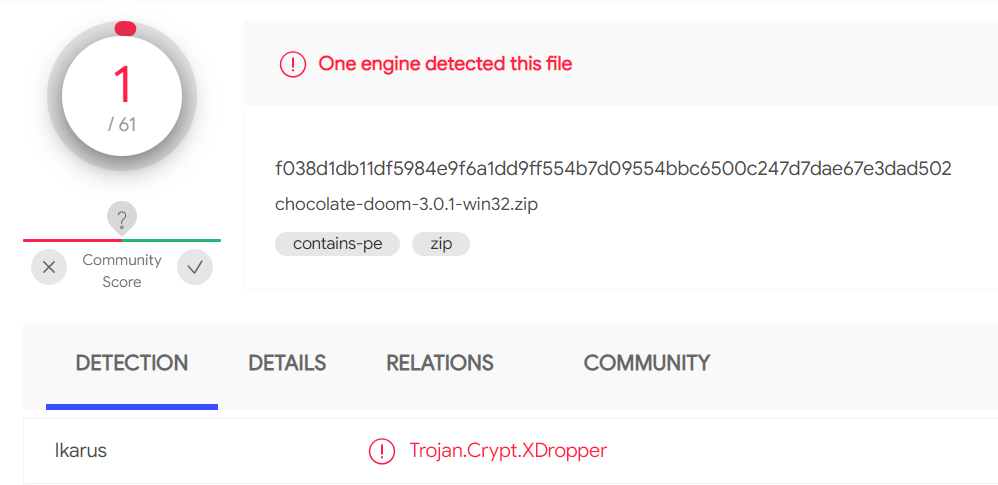 Chocolate Doom 3.0.1 might have a virus - Doom General - Doomworld07 junho 2024
Chocolate Doom 3.0.1 might have a virus - Doom General - Doomworld07 junho 2024 -
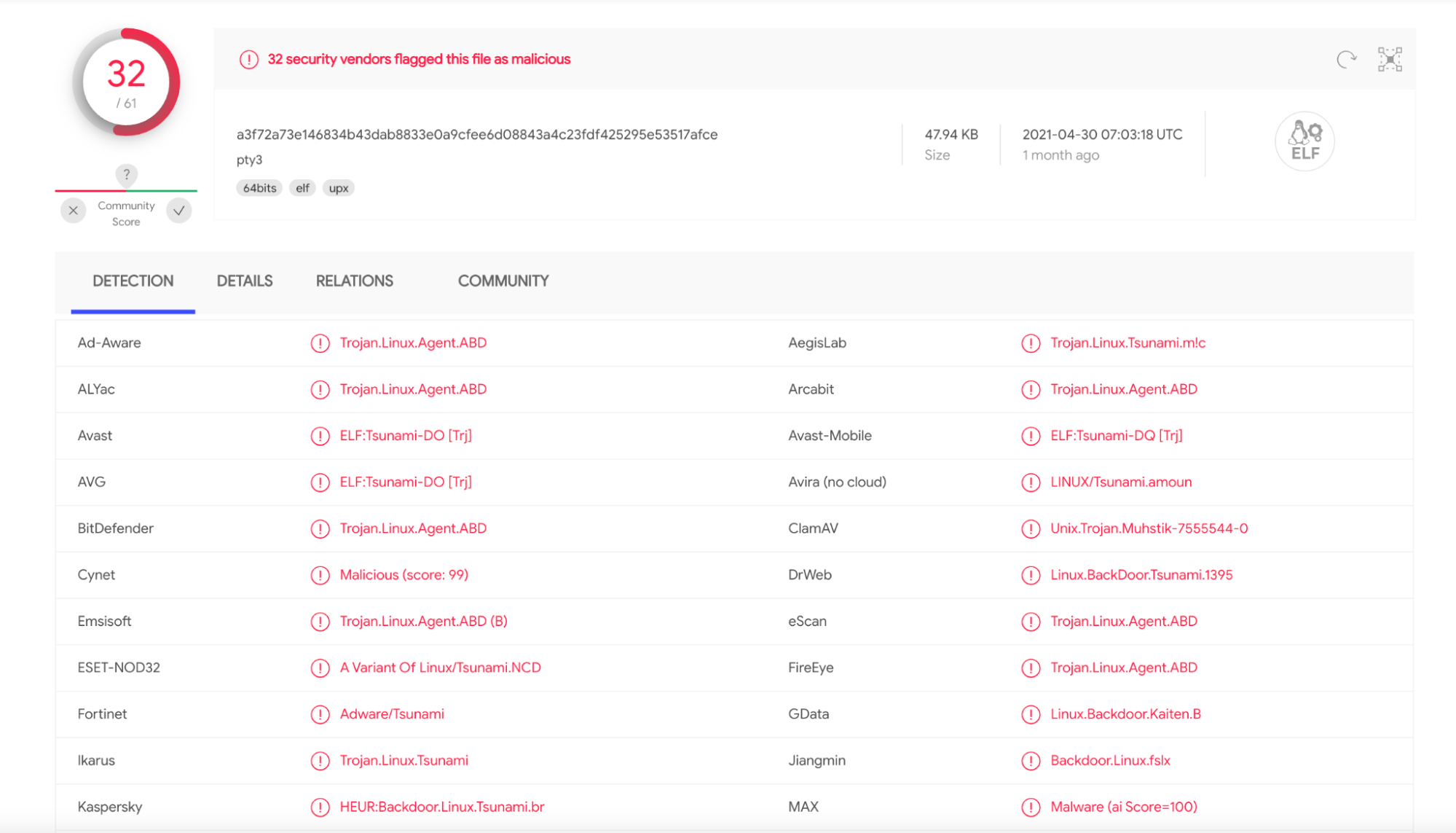 Hands-On Muhstik Botnet: crypto-mining attacks targeting Kubernetes – Sysdig07 junho 2024
Hands-On Muhstik Botnet: crypto-mining attacks targeting Kubernetes – Sysdig07 junho 2024 -
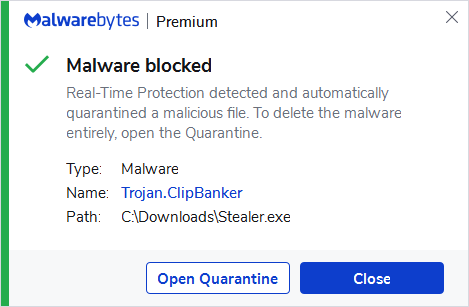 Trojan.ClipBanker07 junho 2024
Trojan.ClipBanker07 junho 2024
você pode gostar
-
![Favorites Gallery for SynthwaveSurfin -- Fur Affinity [dot] net](https://t.furaffinity.net/53208389@300-1691438690.jpg) Favorites Gallery for SynthwaveSurfin -- Fur Affinity [dot] net07 junho 2024
Favorites Gallery for SynthwaveSurfin -- Fur Affinity [dot] net07 junho 2024 -
 Animating with Scratch07 junho 2024
Animating with Scratch07 junho 2024 -
The rogues gallery at police headquarters - NYPL Digital Collections07 junho 2024
-
Cartoony Angry Face's Code & Price - RblxTrade07 junho 2024
-
 Bubble Skincare's New Morning Rays Eye Cream Brightens & De-puffs – StyleCaster07 junho 2024
Bubble Skincare's New Morning Rays Eye Cream Brightens & De-puffs – StyleCaster07 junho 2024 -
 Jogo Faça Face Monte Suas Carinhas Infantil Muito Divertido07 junho 2024
Jogo Faça Face Monte Suas Carinhas Infantil Muito Divertido07 junho 2024 -
 Conheça a franquia “Another”07 junho 2024
Conheça a franquia “Another”07 junho 2024 -
 Shadow arrived to save Alexia Kage no Jitsuryokusha ni Naritakute!07 junho 2024
Shadow arrived to save Alexia Kage no Jitsuryokusha ni Naritakute!07 junho 2024 -
 West Fork Trail West Virginia Rails To Trails07 junho 2024
West Fork Trail West Virginia Rails To Trails07 junho 2024 -
 Wallpaper : 4k, cyberpunk, cyber city, futuristic city 3840x163407 junho 2024
Wallpaper : 4k, cyberpunk, cyber city, futuristic city 3840x163407 junho 2024