Cryptographic Keys 101: What They Are & How They Secure Data - Hashed Out by The SSL Store™
Por um escritor misterioso
Last updated 16 junho 2024

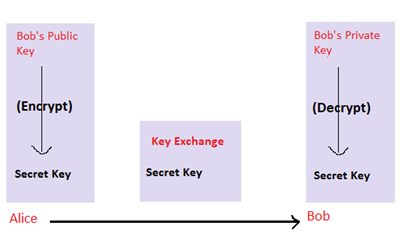
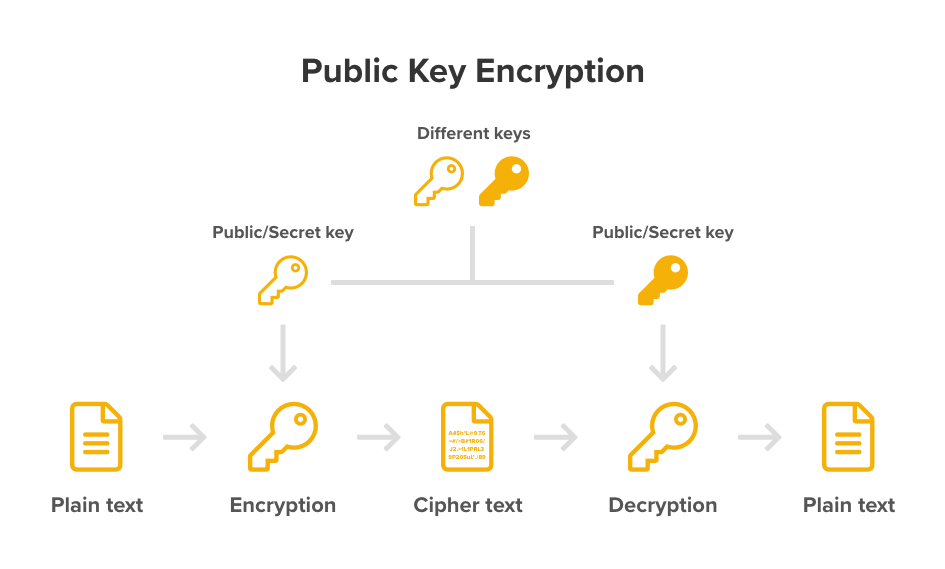
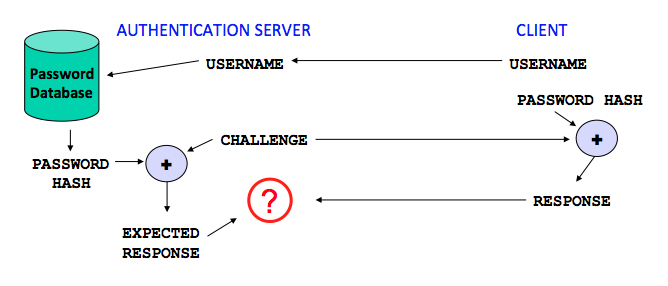
Cryptographic keys, in combination with an encryption algorithm, disguise data (encryption) so only a special key can access it (decryption).
Cryptography 101 with SSL
The SSL Store: What Is a TPM in Security? Trusted Platform Modules

An Overview of Cryptography

Future Solutions Poster - Cybersecurity, PDF, Encryption

Quantum Computing Just Took a Big Step Forward - Hashed Out by The
Cryptography 101
An Overview of Cryptography
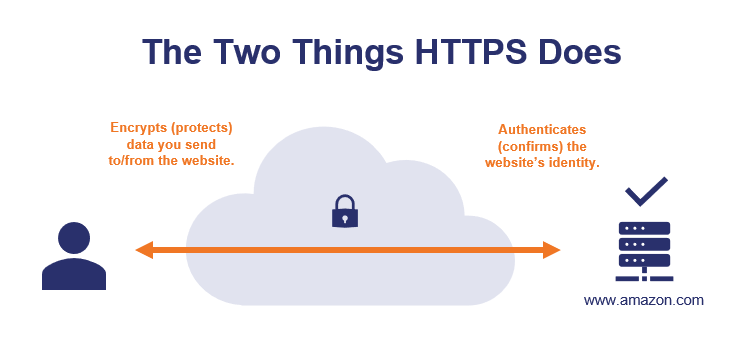
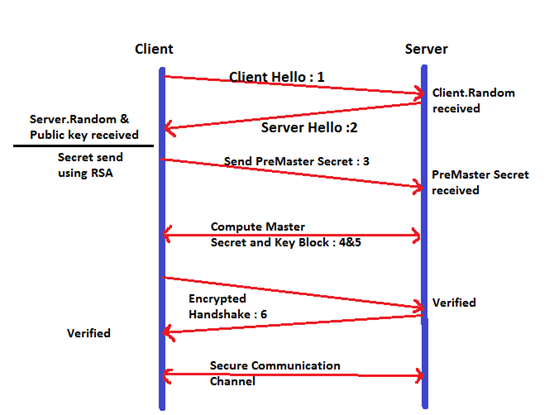
How Does HTTPS Work? - Security Boulevard
Cryptography 101 with SSL

PII Encryption Protect Your Customer's Privacy
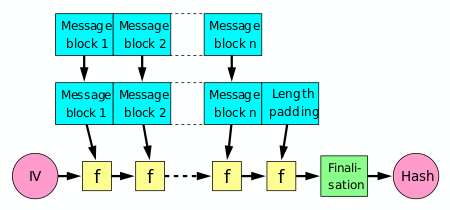
Cryptographic hash function - Wikipedia
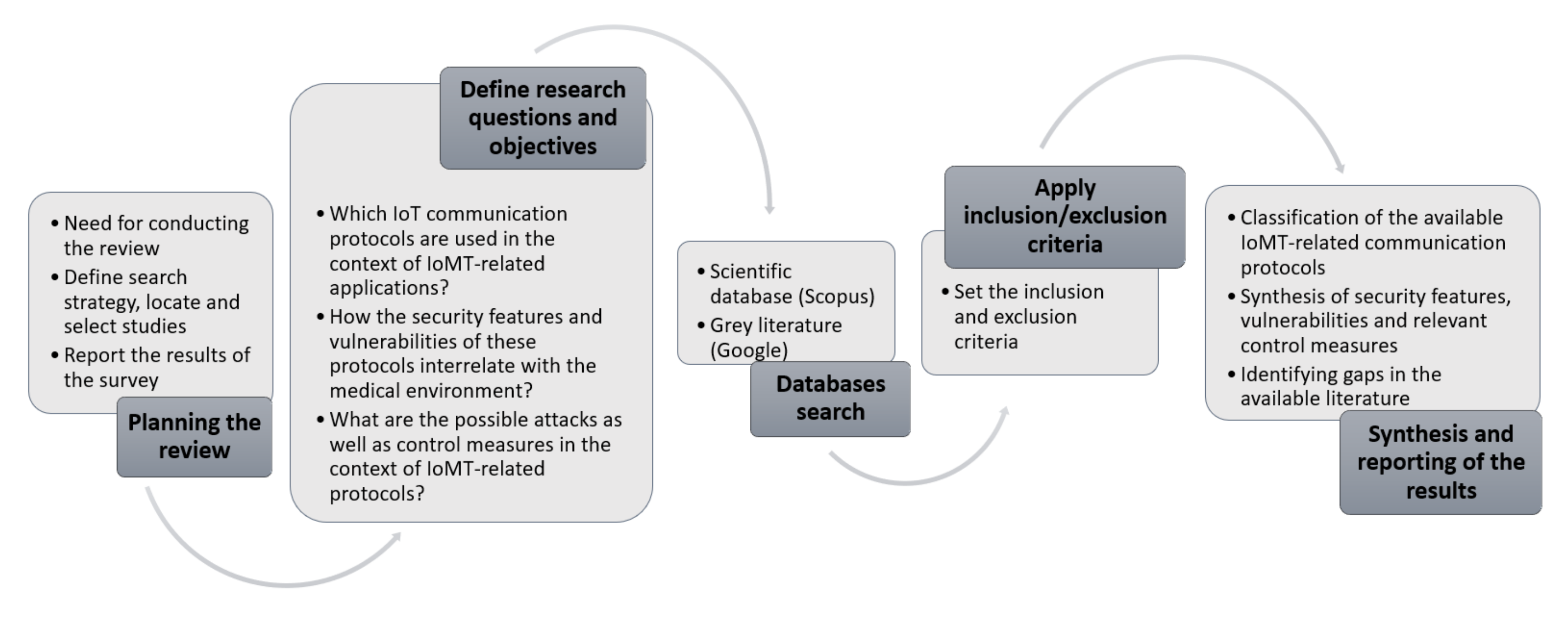
Sensors, Free Full-Text
Recomendado para você
-
 Lock and key - Wikipedia16 junho 2024
Lock and key - Wikipedia16 junho 2024 -
Keys for Safety Storage Cabinets16 junho 2024
-
 Dog Door Keys, Accessories16 junho 2024
Dog Door Keys, Accessories16 junho 2024 -
 Lost Keys Goodwill Vehicle Donations16 junho 2024
Lost Keys Goodwill Vehicle Donations16 junho 2024 -
Titan Security Key - FIDO2 USB-A/USB-C + NFC16 junho 2024
-
 How to Recycle Keys or Put Them to Good Use16 junho 2024
How to Recycle Keys or Put Them to Good Use16 junho 2024 -
 Federal 6Y-series Keys Cut Online TODAY - We Love Keys16 junho 2024
Federal 6Y-series Keys Cut Online TODAY - We Love Keys16 junho 2024 -
 Keys, Charlotte, NC Eastway Lock & Key, Inc.16 junho 2024
Keys, Charlotte, NC Eastway Lock & Key, Inc.16 junho 2024 -
 Does AutoZone Cut Keys? - AutoZone16 junho 2024
Does AutoZone Cut Keys? - AutoZone16 junho 2024 -
 Alicia Keys Wants to Be Your New Self-Care Mentor, Cover Interview16 junho 2024
Alicia Keys Wants to Be Your New Self-Care Mentor, Cover Interview16 junho 2024
você pode gostar
-
 NARUTO SHIPPUDEN: Ultimate Ninja STORM 4 ROAD TO BORUTO16 junho 2024
NARUTO SHIPPUDEN: Ultimate Ninja STORM 4 ROAD TO BORUTO16 junho 2024 -
 PPT - Which Free Solitaire Game Is The Best? PowerPoint Presentation, free download - ID:1195666816 junho 2024
PPT - Which Free Solitaire Game Is The Best? PowerPoint Presentation, free download - ID:1195666816 junho 2024 -
 Filme de Uncharted: diretor fala sobre ideias para sequência16 junho 2024
Filme de Uncharted: diretor fala sobre ideias para sequência16 junho 2024 -
 Vôlei - O Guia Completo - Clube Paineiras Do Morumby16 junho 2024
Vôlei - O Guia Completo - Clube Paineiras Do Morumby16 junho 2024 -
 The Last of Us Season 2: How will the HBO series handle the games16 junho 2024
The Last of Us Season 2: How will the HBO series handle the games16 junho 2024 -
 Liga MX 2023: ¿Cuántas estrellas tiene Tigres? Títulos y campeonatos en su historia16 junho 2024
Liga MX 2023: ¿Cuántas estrellas tiene Tigres? Títulos y campeonatos en su historia16 junho 2024 -
 West Mifflin police looking for suspect in armed robbery16 junho 2024
West Mifflin police looking for suspect in armed robbery16 junho 2024 -
 LoL Patch 13.19 patch notes All buffs, nerfs, and changes in the League Worlds 2023 update - Dot Esports16 junho 2024
LoL Patch 13.19 patch notes All buffs, nerfs, and changes in the League Worlds 2023 update - Dot Esports16 junho 2024 -
 Moto Cram Grau Cup Logo PNG Vector (EPS) Free Download16 junho 2024
Moto Cram Grau Cup Logo PNG Vector (EPS) Free Download16 junho 2024 -
 Organic Sicilian Lemon Almonds/International Harvest/Dried Fruits, Nuts & Seeds – igourmet16 junho 2024
Organic Sicilian Lemon Almonds/International Harvest/Dried Fruits, Nuts & Seeds – igourmet16 junho 2024
